What’s happening when sending an email?
Find out about the history and the mechanisms put together to create and send an email! Explanations & infographics next!

Find out about the history and the mechanisms put together to create and send an email!
Explanations & infographics next!
Some history first…
The invention of emailing in 1971 finds its origins within the creation of the ARPANET network. Its inventor Ray Tomlinson is a graduated engineer from the prestigious MIT (Massachusetts Institute of Technology). As a big part of our everyday life, the email is indeed one of the greatest inventions of our time.
Before it was possible to send messages but they were exchanged only between users of the same domain name and on the same device.
Those restrictions were therefore considerably reducing the emailing’s possibilities.
Ray Tomlinson idea was to create sending and receiving protocols using the ARPAnet network. Some applications had previously been created but were only dedicated to sending and reading messages.
One thing was missing at that point: a way to differentiate the user name from the domain name to guide the device delivering the mail. That is how the email address as we know it today was born, separated with an at-sign (@).
Why using this at-sign? Ray Tomlinson found that this sign was not use in any fist name, neither was it in any company’ name.
Let’s find out first the mechanisms put together by Mr Tomlinson to create the email, then take a look at the different steps that happens when you are sending an email.
Understanding the exchange of information
First, it is important to understand the structures allowing the exchange of information. Several levers exist and constitute the network architecture.
a) Network & IP
Emails exist and pass through a computer network. This network is in reality made of computers that transport information but also recognize one another.
To recognize each other, those devices have an IP assigned. This IP is made of a series of numbers that act as an “ID card”. A computer owns an IP address of its own such as a website for example.
IP addresses are always looking this way: 218.95.135.170
Websites have IP addresses managed by DNS servers (Domain Name Server) that indicate the address at which the site is published. So, when you want to display a website in your browser, your computer queries that server to find out where the URL you want to reach is.
b) Servers & protocols
Let’s go back to those servers for a second. We mentioned earlier the role of DNS servers in establishing the “dialogue” between website and computer. There are many types of servers that can respond to specific requests.
In this article we will be particularly interested in the servers in place during the email sending process.
The servers specific to the sending and receiving of emails, have a function similar to the Post Office. They guarantee the formatting, control and transfer of the message from the sender to the recipient.
Protocols represent the flows that allow two servers to communicate with each other. Depending on requests and servers, specific protocols are used. For example, when sending an email, we use the SMTP protocol (Simple Mail Transfer Protocol) while to retrieve an email, it is the IMAP protocol (Internet Message Access Protocol) or POP (Post Office Protocol) that applies.
Now that we have fully grasped the various players in a process of sending mail, it remains only to understand the steps that structure this standardized action.
Steps in sending an email
a) Writing and conversion
First of all, when you decide to write an email, you must open an email client. This service can either be located locally on your computer via email software (Thunderbird, Outlook, Mail, etc.) or online through email services (Gmail, Hotmail, etc.).
These email clients are called in the computer jargon the MUA (Mail User Agent).
So, it is this email client that allows you to initially write your emails but also to receive them.
The route of an email can be summarized in those three words:
• Formatting
• Control
• Transfer
Let’s find out the route that it operates once written.
b) Sending and control


Once the email is written, you click on “send” and the journey begins. The message is formatted by the mail client (MUA) in order to be recognizable by the SMTP protocol (mail sending protocol).
What is this formatting?
This involves separating the message into two parts:
- The header of the text which includes the information relating to the sender, the date and time of dispatch, the subject of the message and the information of the recipient(s) of this email.
- The body of the text that groups the content of the email as well as other forms of content such as attachments.
Your email client then sends the message to the email server: the SMTP server.
This server is the backbone of the email service.
Its role is twofold: it checks the e-mails sent and finds the server corresponding to the recipient’s email address.
Control is a big part of the process of sending an email since if this phase is not approved, the mail returns directly to the sender with an error message. The control is based on various points, including the maximum size allowed, the volume of attachments, malware surveillance (virus, Trojan horse, SPAMS detection, etc.). If the message complies with the sender’s mail server requirements, it is sent to the recipient’s mail server.
How is the recipient’s email address identified? Or rather, how do mail servers manage to determine where to send the message?
Once checked, the server queries the DNS service in order to obtain the list of mail servers of the recipient’s domain name.
One of these servers, called MX servers responds and gives the location of the mailbox.
Once the box is found, the message is transferred to the recipient MX server.
This server performs a second control phase with its own standards assigned to maximum message sizes and attachments and its own filters assigned to spam before storing the message in the box.
c) Retrieval of mail

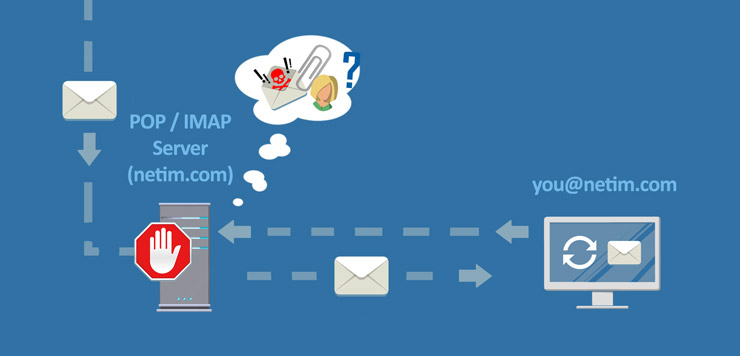
Once the email is transmitted and controlled by the recipient’s MX server, it is stored on the mail server and ready to be retrieved.
The recipient’s Mail Client (MUA (Mail User Agent)) queries the Mail Server in order to retrieve the message content. The content is again checked by the Mail Server to detect spam or malware.
The different control steps during the process of sending or retrieving e-mails may seem tedious at first glance but are actually there to protect users from fraudulent messages.
What is most impressive here is the speed with which this process is carried out. In fact, most of these controls take in all and for all only a few seconds.
The last word…
Email is a tool that we use all the time and, like many of the mechanisms we have adopted regarding web technology, we often do not know the technical processes surrounding these practices.
Messaging services are constantly evolving in order to offer ever more innovative experiences to users. Recently, Gmail announced the implementation of its AMP technology allowing emails to become interactive and dynamic.
The email still has beautiful days ahead on the eve of its 50th birthday!








